Malware operations focusing on holders of Ethereum, XRP, and Solana cryptocurrencies have been uncovered by cybersecurity researchers. The menace assaults Atomic and Exodus pockets house owners by utilizing compromised software program packages put in by builders unaware of the malware contained within the code.
The malware, upon execution, is ready to ship cryptocurrency to thief-held addresses with no indication on the pockets proprietor.
How The Assault Works
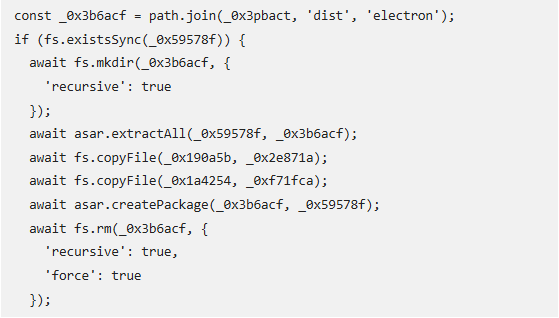
Researchers say the assault begins when builders unwittingly embrace hacked node bundle supervisor (NPM) packages of their initiatives. One such bundle named “pdf-to-office” seems real on the floor however conceals malicious code inside.
The bundle searches computer systems for put in crypto wallets after which injects code that intercepts transactions. This permits criminals to steal cash with out the person’s consciousness or permission.
A number of Cryptocurrencies At Threat
Safety researchers have concluded that the malware can divert transactions on a number of of the world’s main cryptocurrencies. They embrace Ethereum, USDT, XRP and Solana. The assault is what researchers establish as “an escalation within the ongoing focusing on of cryptocurrency customers via software program provide chain assaults.”
Technical Particulars Reveal Refined Strategies
ReversingLabs found the marketing campaign by scanning for suspicious NPM packages. Their evaluation revealed a number of warning indicators comparable to suspicious URL associations and code constructions matching well-known threats.
The assault employs refined methods for evasion from safety instruments and is multi-stage in nature. The an infection begins when the malware bundle executes its code geared toward pockets software program on the goal’s machine. It particularly appears for software recordsdata in among the predetermined paths earlier than injecting its malicious code.
No Visible Person Warning Indicators
In keeping with studies, this malware’s impact may be catastrophic since transactions seem completely regular on the pockets interface. The code substitutes legitimate recipient addresses with attacker-controlled addresses via base64 encoding.
For example, when a person makes an attempt to ship ETH, the malware substitutes the recipient handle with the attacker’s handle, which is hid in encoded kind. Customers haven’t any visible clue that something is flawed till they verify the blockchain document afterward and uncover their cash went to an sudden handle.
The safety menace signifies elevated hurt to cryptocurrency house owners who won’t remember their transactions are compromised till funds go lacking. The modus operandi of the assault is proof of how hackers maintain developing with new strategies of pilfering digital belongings.
Cryptocurrency customers must be extraordinarily cautious when verifying all transaction addresses. Builders are additionally suggested to double-check the safety of any packages they set up on cryptocurrency-related initiatives.
Featured picture from Enterprise Networking Planet, chart from TradingView